Modern technology has changed every part of our lives, and the need to prove one’s identity, “Identity Verification“, remains steadfast. Whether swiping a credit card, accessing a bank account, or enjoying a glass of wine, identity verification is the bedrock of trust in transactions.
It safeguards the individual and the business, ensuring a seamless exchange of goods and services. However, the transition to digital transactions has posed new challenges, demanding innovative solutions to uphold the integrity of identity verification.
Identity Verification Development

In an era marked by digital interactions, traditional identity verification methods face a new set of hurdles. Manual identification processes can lead to cumbersome customer experiences and jeopardize businesses’ reputations and financial stability.
This is where digital identity verification steps in, emerging as a crucial component of modern businesses’ digital transformation endeavors.
This transformation isn’t just about embracing technology; it’s about ensuring a secure, frictionless, and trustworthy digital experience for customers.
What Is Digital Identity Verification?
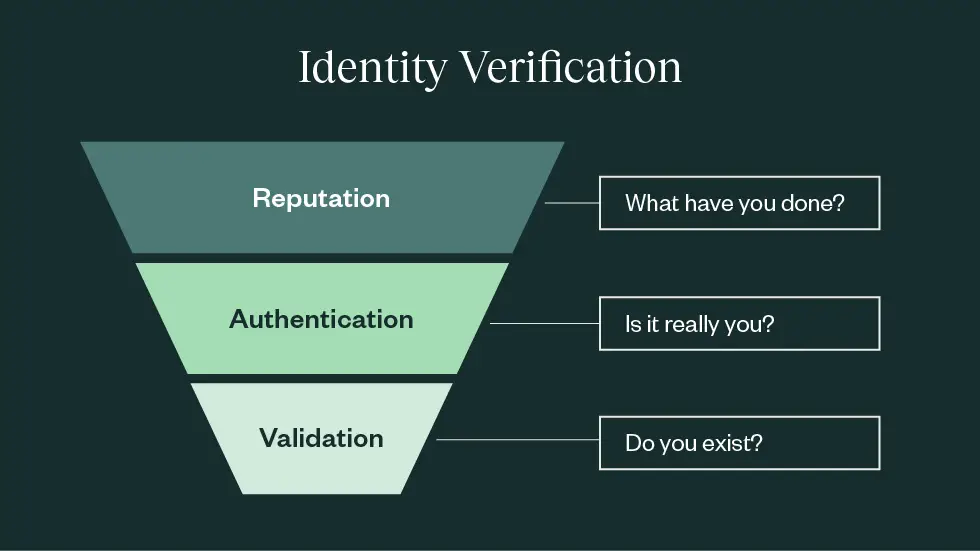
At its core, identity verification in business transactions entails authenticating and validating an individual’s identity before a sensitive transaction occurs. In the digital realm, this process assumes a new form known as digital identity verification.
As more transactions shift online, ensuring secure digital experiences becomes paramount, particularly in the context of signing agreements.
What Are The Methods Of Identity Verification?
Identity verification can take either manual or automated routes, contingent on the transaction type and method employed:
- Manual Verification: Traditional identification methods involve presenting physical documents, which are then compared against the person and cross-referenced with available public databases.
- Electronic Verification: Online transactions often necessitate additional layers of validation due to the lack of physical presence. An initial email verification might suffice, while high-value or risk-prone transactions might demand multi-factor authentication.
Benefits of Digital Identity Verification
Embracing digital identity verification reaps numerous rewards for businesses and customers alike:
- Enhanced User Experience: Simplifying application processes and securing sensitive information creates a seamless user journey, eliminating stress and boosting satisfaction.
- Fraud Mitigation: Digital identity verification thwarts fraudulent applications, safeguarding businesses from financial losses and customers from identity theft.
- KYC Compliance: Adhering to Know Your Customer (KYC) regulations is imperative in the financial sector. Digital identity verification ensures businesses meet these ethical standards.
- Automated Efficiency: Automated data extraction and verification minimize the need for manual data entry, expediting the verification process and minimizing risks.
What Are the Methods of Digital Identity Verification?

Several methods drive digital identity verification:
- Government-Issued Photo ID: Capturing an ID photo or even a real-time selfie verifies an individual’s identity.
- Bank Login Credentials: Secure integrations with financial institutions allow users to authenticate their identity by logging into their bank accounts during the application process.
- Facial Biometric Technology: Advanced algorithms analyze facial images, comparing them against datasets to ascertain their authenticity.
- Knowledge-Based Authentication (KBA): Applicants answer personalized questions to verify their identity based on identifiable credit profile information.
- Two-Factor Authentication: Customers enter a secure code via email or SMS for verification.
- Digital Footprint Analysis: Online activity linked to email addresses and phone numbers validates identity using social media data.
- Online Notarization: Services like Notarize facilitate online identity verification through live notaries, balancing customer experience and fraud prevention.
Understanding and Preventing Digital Identity Theft
In a time when the digital fabric intricately weaves our lives together, identity theft is a constant threat. As our personal information traverses cyberspace, malicious actors seize opportunities to exploit vulnerabilities, potentially wreaking havoc on our lives.
This digital-era crime, digital identity theft, demands our vigilant attention and proactive measures to safeguard our most valuable asset: our identity.
What Is Digital Identity Theft?
Digital identity theft is a contemporary manifestation of an age-old crime where perpetrators steal sensitive personal information to impersonate victims online.
Unlike traditional theft, where physical possessions are stolen, digital identity theft targets information – a resource that, when breached, can unravel an individual’s life, both financially and emotionally.
Cybercriminals use hackers, phishing scams, and data breaches as tools to compromise identities and exploit them for personal gain.
The Dangers of Digital Identity Theft

The ramifications of digital identity theft are far-reaching and profound, affecting victims on multiple fronts:
- Financial Ruin: Cybercriminals can exploit stolen identities to gain unauthorized access to financial accounts, siphoning funds, incurring debt, and damaging credit scores.
- Emotional Toll: Victims often endure emotional distress as they navigate the aftermath of identity theft, feeling violated and powerless.
- Stolen Reputation: Digital identity theft can tarnish an individual’s reputation, mainly if their identity is used for fraud.
- Legal Implications: Victims may find themselves entangled in legal battles to prove their innocence and rectify the damage caused by cybercriminals.
- Privacy Invasion: Personal information, once stolen, can be used for blackmail, extortion, or even to perpetrate cyberbullying.
Preventing the Perpetuation of Digital Identity Theft
The quest to prevent digital identity theft necessitates a multi-pronged approach, combining vigilance, cybersecurity best practices, and education.
- Strengthen Passwords: Craft solid and unique passwords for each online account, employing a mix of upper and lower-case letters, numbers, and special characters.
- Multi-Factor Authentication (MFA): Enable MFA wherever possible to add an extra layer of security, requiring multiple forms of verification for access.
- Beware of Phishing: Exercise caution when clicking links or providing personal information via email. Verify the sender’s legitimacy before responding.
- Secure Networks: Use secure, encrypted networks for online transactions and avoid public Wi-Fi for sensitive activities.
- Regular Updates: Keep operating systems, software, and antivirus programs up to date to protect against vulnerabilities.
- Monitor Financial Activity: Regularly review financial statements for unauthorized transactions and set up alerts for suspicious activities.
- Limit Sharing: Be cautious about sharing personal information on social media platforms and websites, as cybercriminals can exploit this data.
- Secure Personal Devices: Ensure that smartphones, tablets, and computers are password-protected and equipped with security software.
- Data Encryption: Use encryption tools for sensitive files and data, making it challenging for unauthorized individuals to access them.
- Educate Yourself: You can protect yourself from possible threats by staying current on the latest cyber threats and scams.
Secure Digital Footprint
In a hyper-connected world, the battle against digital identity theft extends beyond individual efforts.
Governments, businesses, and individuals must collaborate to create a secure digital ecosystem that protects our identities.
Robust cybersecurity measures, stringent regulations, and continuous education are essential to thwart cybercriminals and ensure that our digital identities remain our most closely guarded possession.
Through collective vigilance and resilience, we can navigate the digital landscape with confidence, shielding our identities from the perils of digital identity theft.
Conclusion: Digital Identity Verification
In a landscape rife with digital identity theft, achieving equilibrium between customer experience and fraud prevention is paramount.
Notarize revolutionizes identity verification through its online platform, offering seamless notarizations. This allows companies to give their customers the best digital experiences possible while lowering the risk of scams. This shows how important trust and safety are in the digital age.
Discover more from Digital Wealth Guru
Subscribe to get the latest posts sent to your email.







Comments